practice exams:
Pass Microsoft 365 MS-500 Exam in First Attempt Easily
Real Microsoft 365 MS-500 Exam Questions, Accurate & Verified Answers As Experienced in the Actual Test!
Microsoft MS-500 Practice Test Questions, Microsoft MS-500 Exam Dumps
Passing the IT Certification Exams can be Tough, but with the right exam prep materials, that can be solved. ExamLabs providers 100% Real and updated Microsoft 365 MS-500 exam dumps, practice test questions and answers which can make you equipped with the right knowledge required to pass the exams. Our Microsoft MS-500 exam dumps, practice test questions and answers, are reviewed constantly by IT Experts to Ensure their Validity and help you pass without putting in hundreds and hours of studying.
Microsoft MS-500 Practice Test Questions, Microsoft MS-500 Exam Dumps
The Microsoft MS-500 exam, formally titled Microsoft 365 Security Administration, is a certification that validates a professional's ability to implement, manage, and monitor security and compliance solutions across the Microsoft 365 environment. It covers a wide range of security disciplines, including identity and access management, threat protection, information protection, and compliance management. Organizations that rely on Microsoft 365 need qualified administrators who can configure these security capabilities correctly, and the MS-500 certification serves as the industry-recognized benchmark for that competency.
The exam is designed for security administrators who work with Microsoft 365 services on a daily basis and who are responsible for protecting their organization's data, users, and infrastructure from a constantly evolving threat landscape. Candidates must demonstrate the ability to work with tools like Microsoft Defender, Azure Active Directory, Microsoft Purview, and Microsoft Sentinel, among others. The breadth of the exam reflects the breadth of the security administrator role itself, which touches virtually every layer of the Microsoft 365 stack. Earning this certification communicates to employers that you have the knowledge and judgment to manage enterprise security at a level that genuinely matters in practice.
Why Practice Tests Are Essential
Practice tests are among the most valuable resources available to any MS-500 candidate, and their importance goes well beyond simple familiarity with question formats. Working through practice questions forces active recall, which is one of the most well-documented techniques for consolidating knowledge in long-term memory. When you read a study guide, your brain processes information passively. When you answer a practice question, your brain must retrieve and apply that information under conditions that closely resemble the actual exam. This retrieval effort is precisely what strengthens the neural pathways that make knowledge accessible when it matters most.
Beyond memory consolidation, practice tests serve as a diagnostic tool that identifies specific knowledge gaps before they become costly mistakes on the actual exam. A candidate who completes a set of practice questions and reviews every incorrect answer honestly will develop a precise map of the areas where their preparation is weakest. This information transforms the subsequent study sessions from broad review into targeted remediation, dramatically improving the efficiency of the remaining preparation time. Candidates who skip this diagnostic phase and simply re-read the same material repeatedly often arrive at the exam with blind spots they never knew existed, because passive review rarely surfaces gaps the way active testing does.
Identity and Access Management Topics
Identity and access management represents one of the largest and most heavily tested domains in the MS-500 exam. This domain covers the configuration and management of Azure Active Directory, which is the identity foundation for all Microsoft 365 services. Candidates must understand how to implement and manage multi-factor authentication, configure conditional access policies that enforce access requirements based on user, device, location, and application risk signals, and manage privileged identities using Azure AD Privileged Identity Management. Each of these capabilities plays a critical role in protecting organizational resources from unauthorized access.
Practice questions in this domain frequently test your ability to reason through realistic scenarios in which you must select the most appropriate identity configuration to meet a specific security requirement. For example, a question might describe an organization that wants to require multi-factor authentication only for users accessing sensitive applications from outside the corporate network, and ask you to identify the correct conditional access policy configuration. Answering these questions correctly requires not just knowing what each feature does in isolation but understanding how the features interact and which combination of settings produces the desired security outcome without unnecessarily restricting legitimate user access.
Threat Protection Knowledge Areas
The threat protection domain of the MS-500 exam covers the Microsoft Defender suite of products and their role in detecting, investigating, and responding to security threats across the Microsoft 365 environment. Microsoft Defender for Office 365 protects email and collaboration tools from phishing, malware, and other mail-based attacks through capabilities like Safe Links, Safe Attachments, and anti-phishing policies. Microsoft Defender for Endpoint provides endpoint detection and response capabilities that monitor device behavior for signs of compromise and enable security teams to investigate and contain threats on managed devices.
Practice questions in this area often present security incidents or configuration scenarios that require you to identify the correct tool, setting, or response action. You might be asked to determine which Defender for Office 365 policy would protect users from a specific type of phishing attack, or to identify the correct sequence of steps for investigating a compromised device using Defender for Endpoint. Developing fluency with the specific capabilities, configuration options, and terminology of each Defender product is essential for performing well in this domain. Candidates who conflate the capabilities of different Defender products or who are uncertain about which product addresses which type of threat will find this section of the exam particularly challenging.
Information Protection and Governance
Information protection is the domain of the MS-500 exam that covers how organizations classify, label, and protect sensitive data across Microsoft 365. Microsoft Purview Information Protection provides the tools through which administrators define sensitivity labels that classify content according to its sensitivity level, configure label policies that deploy those labels to users, and apply protection settings like encryption and access restrictions that travel with labeled content wherever it goes. This approach to data protection is particularly powerful because it is content-centric rather than location-centric, meaning that protection follows the data even when it leaves the organization's controlled environment.
Practice test questions in this domain frequently involve scenarios in which you must design or evaluate a labeling strategy for a given organizational requirement. For instance, a question might describe a company that needs to ensure that all documents containing financial data are automatically encrypted when shared externally, and ask you to identify which combination of sensitivity label settings and auto-labeling policy configuration would accomplish this. Answering such questions correctly requires a thorough understanding of how sensitivity labels, label policies, trainable classifiers, and auto-labeling rules work together as a system, not just an isolated knowledge of each component.
Compliance Management Fundamentals
The compliance management domain of the MS-500 covers Microsoft Purview's compliance tools and how they are used to help organizations meet their legal, regulatory, and policy obligations. Data Loss Prevention policies are a central topic in this domain. These policies detect and prevent the sharing of sensitive information, such as credit card numbers, social security numbers, or proprietary business data, through email, Teams messages, SharePoint sites, and other Microsoft 365 channels. Administrators configure DLP policies by defining the types of sensitive information they protect, the conditions under which the policy triggers, and the actions the policy takes when a violation is detected.
Retention policies and retention labels are another major compliance topic that the MS-500 exam tests extensively. These tools allow organizations to ensure that important content is preserved for the duration required by regulatory or business requirements and that content past its useful life is disposed of in a controlled and documented manner. Candidates must understand the difference between retention policies, which apply retention settings broadly to entire workloads or locations, and retention labels, which apply retention settings to specific items based on content type or user action. The interaction between retention settings and sensitivity labels, and the precedence rules that govern which setting applies when multiple policies affect the same content, are nuances the exam tests with precision.
Microsoft Sentinel and Security Operations
Microsoft Sentinel is a cloud-native security information and event management solution, commonly called a SIEM, that aggregates security data from across an organization's environment, applies analytics to detect threats, and enables security operations teams to investigate and respond to incidents. For MS-500 candidates, understanding Sentinel at a functional level is increasingly important as the product has become more central to the Microsoft security stack and more frequently appears in exam questions. Key topics include how to connect data sources to Sentinel through connectors, how analytics rules are configured to detect suspicious activity patterns, and how incidents are created and managed in the Sentinel workspace.
Practice questions involving Sentinel often test your ability to reason about detection and response scenarios. A question might describe a security alert and ask you to identify the correct Sentinel feature for automating the response, or it might present a detection rule configuration and ask whether it would correctly identify a specific type of attack. Working through these questions requires a conceptual understanding of how SIEM systems operate, how log data flows from source systems into Sentinel, and how analytics rules transform raw event data into actionable security alerts. Candidates who have had the opportunity to work with Sentinel in a real or lab environment will find these questions considerably more approachable than those who know the product only from documentation.
Secure Score and Security Benchmarks
Microsoft Secure Score is a measurement tool within the Microsoft 365 Defender portal that quantifies an organization's security posture by assigning points for each security control that has been implemented and configured correctly. It provides a prioritized list of recommended actions that administrators can take to improve their score, along with detailed guidance on how to implement each recommendation. For MS-500 candidates, Secure Score is an important concept because it represents how Microsoft thinks about the relative importance of different security configurations and provides a framework for prioritizing security investments.
Practice questions about Secure Score typically test your understanding of how the score is calculated, what kinds of actions improve it, and how it should be used as part of a broader security management strategy. Candidates should understand that Secure Score is a tool for measuring and improving posture over time, not an absolute measure of security that can be taken at face value. A high Secure Score does not guarantee that an organization is immune to attacks. It means that the organization has implemented many of the security controls that Microsoft considers important. Understanding this nuance, and being able to apply it in scenario-based questions, distinguishes candidates with genuine security understanding from those who know only surface-level facts about the tool.
Exam Dumps and Their Real Risks
Exam dumps are collections of questions and answers that claim to represent the actual content of a certification exam, typically compiled from the recollections of candidates who have recently taken the test or obtained through unauthorized means. They circulate widely online, often marketed aggressively to candidates who are anxious about passing and looking for shortcuts. The appeal is obvious. If you could memorize the exact questions and answers that will appear on your exam, you could pass without investing the time and effort that genuine preparation requires. This appeal is precisely what makes exam dumps so dangerous and so counterproductive for serious professionals.
The most immediate risk of relying on exam dumps is that they are frequently inaccurate. Questions are misremembered, answers are wrong, and the explanations provided are often based on misunderstanding rather than genuine knowledge. Microsoft also updates its exams regularly, retiring old questions and adding new ones that reflect the latest developments in the platform, which means that dumps become outdated quickly. Candidates who memorize dump content and then encounter updated questions they have never seen before are left without the foundational understanding needed to reason through unfamiliar scenarios. Beyond the practical risk of failure, using exam dumps violates Microsoft's exam policies and can result in certification revocation and a permanent ban from future Microsoft certification exams, consequences that no serious professional should risk.
Legitimate Practice Test Resources
Legitimate practice tests, by contrast, are designed by subject matter experts who have deep knowledge of the exam's topic areas and who write questions that test genuine understanding rather than simple recall of memorized answers. Microsoft offers official practice tests through its learning partners, and platforms like MeasureUp, Whizlabs, and Pearson VUE provide practice exams that are developed in alignment with the official exam objectives. These resources are valuable not because they predict the exact questions you will see on the exam but because they expose you to the style, format, and level of reasoning that the actual exam demands.
When evaluating practice test resources, quality matters far more than quantity. A set of two hundred well-written practice questions with detailed, accurate explanations is worth far more than a thousand poorly written questions with incorrect or misleading answers. Look for practice tests that include thorough answer explanations that go beyond simply identifying the correct choice and explain why each wrong answer is wrong. This explanatory depth is what transforms a practice test from a simple score measurement tool into a genuine learning resource that builds the understanding and judgment the actual exam tests. Candidates who read every explanation carefully, including for questions they answered correctly, consistently outperform those who focus only on the questions they missed.
Building a Study Plan That Works
A structured study plan is essential for MS-500 preparation because the exam's content breadth makes undirected study inefficient and easy to let slide. Begin by downloading the official MS-500 exam skills outline from Microsoft's certification website and using it as a checklist against which you assess your current knowledge. For each topic area, honestly rate your current level of familiarity and identify the areas where you are starting from the least knowledge. This self-assessment becomes the basis for allocating your study time, directing the most hours to the areas of greatest weakness rather than defaulting to the comfortable habit of spending time on topics you already know reasonably well.
From this baseline, build a weekly schedule that dedicates specific time blocks to specific topic areas and includes regular practice test sessions. A common and effective structure is to spend three to four weeks on content review and skills development, using Microsoft Learn, official documentation, and hands-on lab practice to build genuine competence across the exam's major domains. Follow this with two to three weeks of intensive practice testing, during which you take full-length practice exams under timed conditions, review every question thoroughly, and use your results to identify any remaining knowledge gaps that need targeted attention before the actual exam. This two-phase approach ensures that you arrive at the exam with both the underlying knowledge and the test-taking fluency to perform at your highest level.
Hands-On Lab Practice Importance
Reading about Microsoft 365 security features and actually configuring them in a real environment are fundamentally different experiences, and the MS-500 exam is designed to reward the latter. Many of the exam's questions present scenarios that require you to identify the correct configuration approach for a specific security requirement, and answering these questions correctly requires the kind of practical intuition that only comes from having actually worked through similar configurations yourself. Candidates who have never logged into the Microsoft 365 Defender portal, never created a conditional access policy, and never configured a DLP rule will find scenario-based questions significantly harder than candidates who have done all of these things in a real environment.
Microsoft offers a free thirty-day trial of Microsoft 365, and many of the security features covered in the MS-500 can be explored in a trial tenant at no cost. Microsoft Learn also provides browser-based lab environments called sandboxes for some learning modules that allow you to practice specific configurations without needing your own tenant. Investing time in this hands-on practice is not optional for candidates who want to perform at a high level on the exam. It is the activity that bridges the gap between knowing what a feature does and understanding how to apply it correctly in the kind of realistic, nuanced scenarios that the exam consistently uses to test genuine competency rather than surface-level familiarity.
Time Management During the Exam
The MS-500 exam typically includes between forty and sixty questions and must be completed within a defined time limit that leaves most candidates with roughly one to two minutes per question on average. This time constraint is meaningful but manageable for candidates who have prepared thoroughly. The challenge is not the overall time limit but rather the risk of spending too long on difficult questions and then rushing through easier questions at the end of the exam, which is a pacing error that costs candidates more points than the difficult questions themselves would have.
Developing a disciplined time management strategy during your practice test sessions is the best way to avoid this problem on the actual exam. Practice treating each question as having a budget of approximately ninety seconds. If you are still uncertain after ninety seconds, mark the question for review and move on. Complete all of the questions you can answer with reasonable confidence first, then return to the marked questions with whatever time remains. This approach ensures that you do not leave easy points on the table by running out of time before reaching questions you would have answered correctly. The candidates who perform best on the MS-500 are not always the most knowledgeable. They are often the ones who combine solid knowledge with the disciplined execution that comes from having practiced under realistic time pressure repeatedly before the actual exam.
Conclusion
The Microsoft MS-500 certification represents a genuinely meaningful credential for security professionals working in the Microsoft 365 ecosystem. The knowledge it validates is directly applicable to the daily work of protecting organizational data, managing user identities, detecting and responding to threats, and ensuring that the organization's use of cloud services remains compliant with applicable regulations and internal policies. Employers recognize this credential as evidence that a security administrator has invested the effort required to develop real competence across a broad and technically demanding set of security disciplines.
Preparing for the MS-500 through legitimate means, combining structured content review, hands-on lab practice, and high-quality practice testing, is both the ethically correct approach and the practically superior one. Candidates who earn this certification through genuine preparation arrive with knowledge and skills they can actually use, rather than memorized answers that evaporate the moment the exam ends. The investment in real preparation pays dividends not just on the day of the exam but throughout every subsequent day of professional practice, because the understanding developed through thorough preparation is retained and built upon in ways that shortcut approaches never achieve.
The temptation to rely on exam dumps is understandable but ultimately self-defeating for any professional with genuine career ambitions. The risks of exam dumps include inaccurate content, rapidly outdated questions, and the very real possibility of certification revocation if Microsoft's exam integrity systems detect irregular answer patterns. Beyond these practical risks, there is the more fundamental problem that passing an exam through memorization rather than understanding leaves you unprepared for the actual work the certification claims you can perform. In a field as consequential as security administration, where the quality of your decisions directly affects the safety of your organization's data and the privacy of its users, genuine competence is not optional.
The MS-500 is best approached as an opportunity to develop real security expertise, not as an obstacle to be circumvented by the shortest available path. Candidates who take this longer but more rewarding approach will find that the preparation process itself makes them more capable security administrators, better equipped to protect their organizations and better positioned to continue growing in a field that rewards genuine expertise with both professional recognition and meaningful career advancement.
Choose ExamLabs to get the latest & updated Microsoft MS-500 practice test questions, exam dumps with verified answers to pass your certification exam. Try our reliable MS-500 exam dumps, practice test questions and answers for your next certification exam. Premium Exam Files, Question and Answers for Microsoft MS-500 are actually exam dumps which help you pass quickly.
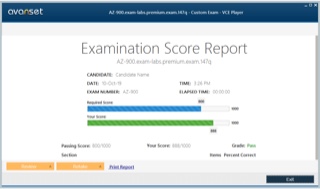
How to Open VCE Files
Please keep in mind before downloading file you need to install Avanset Exam Simulator Software to open VCE files. Click here to download software.
Related Exams
- AZ-104 - Microsoft Azure Administrator
- DP-700 - Implementing Data Engineering Solutions Using Microsoft Fabric
- AZ-305 - Designing Microsoft Azure Infrastructure Solutions
- SC-300 - Microsoft Identity and Access Administrator
- PL-300 - Microsoft Power BI Data Analyst
- MD-102 - Endpoint Administrator
- AI-900 - Microsoft Azure AI Fundamentals
- AB-100 - Agentic AI Business Solutions Architect
- MS-102 - Microsoft 365 Administrator
- AI-102 - Designing and Implementing a Microsoft Azure AI Solution
- AZ-900 - Microsoft Azure Fundamentals
- AB-900 - Microsoft 365 Copilot and Agent Administration Fundamentals
- SC-200 - Microsoft Security Operations Analyst
- AB-730 - AI Business Professional
- SC-401 - Administering Information Security in Microsoft 365
- AZ-700 - Designing and Implementing Microsoft Azure Networking Solutions
- DP-600 - Implementing Analytics Solutions Using Microsoft Fabric
- AB-731 - AI Transformation Leader
- AZ-500 - Microsoft Azure Security Technologies
- SC-100 - Microsoft Cybersecurity Architect
- AZ-204 - Developing Solutions for Microsoft Azure
- GH-300 - GitHub Copilot
- PL-400 - Microsoft Power Platform Developer
- SC-900 - Microsoft Security, Compliance, and Identity Fundamentals
- AZ-140 - Configuring and Operating Microsoft Azure Virtual Desktop
- DP-300 - Administering Microsoft Azure SQL Solutions
- AZ-801 - Configuring Windows Server Hybrid Advanced Services
- AZ-400 - Designing and Implementing Microsoft DevOps Solutions
- AZ-800 - Administering Windows Server Hybrid Core Infrastructure
- PL-600 - Microsoft Power Platform Solution Architect
- PL-200 - Microsoft Power Platform Functional Consultant
- PL-900 - Microsoft Power Platform Fundamentals
- MB-800 - Microsoft Dynamics 365 Business Central Functional Consultant
- MS-700 - Managing Microsoft Teams
- MB-330 - Microsoft Dynamics 365 Supply Chain Management
- DP-900 - Microsoft Azure Data Fundamentals
- MB-310 - Microsoft Dynamics 365 Finance Functional Consultant
- DP-100 - Designing and Implementing a Data Science Solution on Azure
- MB-280 - Microsoft Dynamics 365 Customer Experience Analyst
- AI-300 - Operationalizing Machine Learning and Generative AI Solutions
- AI-103 - Developing AI Apps and Agents on Azure
- MB-820 - Microsoft Dynamics 365 Business Central Developer
- MS-721 - Collaboration Communications Systems Engineer
- MB-230 - Microsoft Dynamics 365 Customer Service Functional Consultant
- MS-900 - Microsoft 365 Fundamentals
- GH-200 - GitHub Actions
- MB-335 - Microsoft Dynamics 365 Supply Chain Management Functional Consultant Expert
- MB-700 - Microsoft Dynamics 365: Finance and Operations Apps Solution Architect
- DP-420 - Designing and Implementing Cloud-Native Applications Using Microsoft Azure Cosmos DB
- GH-900 - GitHub Foundations
- MB-500 - Microsoft Dynamics 365: Finance and Operations Apps Developer
- GH-500 - GitHub Advanced Security
- PL-500 - Microsoft Power Automate RPA Developer
- GH-100 - GitHub Administration
- SC-400 - Microsoft Information Protection Administrator
- AZ-120 - Planning and Administering Microsoft Azure for SAP Workloads
- DP-800 - Developing AI-Enabled Database Solutions
- MB-240 - Microsoft Dynamics 365 for Field Service
- 98-382 - Introduction to Programming Using JavaScript
- MO-200 - Microsoft Excel (Excel and Excel 2019)
- MB-920 - Microsoft Dynamics 365 Fundamentals Finance and Operations Apps (ERP)
- DP-203 - Data Engineering on Microsoft Azure
- 98-383 - Introduction to Programming Using HTML and CSS
- MO-400 - Microsoft Outlook (Outlook and Outlook 2019)
- MS-203 - Microsoft 365 Messaging
- MB-910 - Microsoft Dynamics 365 Fundamentals Customer Engagement Apps (CRM)
- 98-367 - Security Fundamentals
- 98-375 - HTML5 App Development Fundamentals
- 62-193 - Technology Literacy for Educators
- DP-750 - Implementing Data Engineering Solutions Using Azure Databricks
Enter Your Email Address to Proceed
Please fill out your email address below in order to purchase Certification/Exam.
Provide Your Email Address To Download VCE File
Please fill out your email address below in order to Download VCE files or view Training Courses.
-
Trusted By 1.2M IT Certification
Candidates Every Month
-
VCE Files Simulate Real exam
environment
-
Instant download After
Registration