practice exams:
Pass Fortinet NSE4_FGT-7.2 Exam in First Attempt Easily
Real Fortinet NSE4_FGT-7.2 Exam Questions, Accurate & Verified Answers As Experienced in the Actual Test!
Fortinet NSE4_FGT-7.2 Practice Test Questions, Fortinet NSE4_FGT-7.2 Exam Dumps
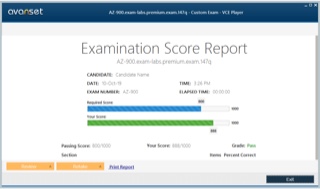
Passing the IT Certification Exams can be Tough, but with the right exam prep materials, that can be solved. ExamLabs providers 100% Real and updated Fortinet NSE4_FGT-7.2 exam dumps, practice test questions and answers which can make you equipped with the right knowledge required to pass the exams. Our Fortinet NSE4_FGT-7.2 exam dumps, practice test questions and answers, are reviewed constantly by IT Experts to Ensure their Validity and help you pass without putting in hundreds and hours of studying.
A Guide to the NSE4_FGT-7.2 Exam and FortiGate Fundamentals
The NSE4_FGT-7.2 certification validates the practical skills required to configure, manage, and troubleshoot FortiGate firewalls within modern enterprise environments. Candidates are expected to demonstrate applied knowledge rather than simple memorization, emphasizing real-world deployment scenarios and network defense strategies. Core competencies include understanding traffic flow, routing behavior, authentication methods, and the interaction between firewall rules and security profiles. Professionals pursuing this credential often align their preparation with evolving data-driven security models discussed in major big data companies, as organizations increasingly rely on intelligent analytics to anticipate threats. This certification serves as a strong foundation for network security careers because it proves the ability to protect digital infrastructure while maintaining operational efficiency.
Evaluating Emerging Threat Trends
Cyber threats evolve continuously, making it essential for security professionals to remain informed about new attack techniques. Regular research and participation in professional communities help administrators anticipate risks before they become widespread. Trend evaluation encourages strategic investment in tools capable of countering sophisticated adversaries. By translating threat intelligence into actionable policy improvements, organizations maintain adaptive defenses that remain effective despite shifting attacker behavior.
Leadership Skills For Security Professionals
Technical expertise becomes even more valuable when paired with strong leadership abilities. Security professionals often guide cross-functional teams, communicate risks to executives, and influence strategic planning. Effective leaders translate complex concepts into clear recommendations that support informed decision-making. They also cultivate collaboration, ensuring that security aligns with broader organizational objectives. As cybersecurity grows increasingly integral to business success, leadership capabilities position professionals to drive meaningful progress while reinforcing a culture of accountability and innovation.
Why FortiGate Knowledge Matters In Modern Security
Cybersecurity landscapes have transformed significantly, requiring administrators to adopt integrated defense mechanisms rather than isolated tools. FortiGate operates as a next-generation firewall capable of deep packet inspection, automated threat response, and centralized policy enforcement. Security professionals benefit by understanding how artificial intelligence enhances detection capabilities, a concept explored across industries adopting AI business transformation to strengthen resilience. Mastery of FortiGate enables organizations to respond rapidly to emerging vulnerabilities while maintaining consistent access control. As enterprises expand across hybrid infrastructures, administrators who understand adaptive security platforms become indispensable contributors to organizational stability.
Exam Structure And Candidate Expectations
The NSE4_FGT-7.2 exam typically includes multiple-choice questions designed to test administrative judgment and technical precision. Candidates should expect scenario-based problems that evaluate their ability to configure policies, diagnose connectivity issues, and implement secure communication channels. Success requires disciplined preparation supported by evidence-driven decision-making, echoing the strategic value emphasized in big data analytics importance across technology ecosystems. Effective candidates focus on understanding system behavior rather than memorizing commands. This mindset allows professionals to adapt quickly when confronted with unfamiliar network conditions during the exam.
Core Networking Foundations For FortiGate
A solid grasp of networking fundamentals remains essential before advancing into firewall configuration. Administrators must understand IP addressing, subnetting, VLAN segmentation, routing protocols, and packet lifecycle processes to anticipate how traffic interacts with security rules. Reliable infrastructure also depends on selecting stable platforms similar to those evaluated among top hosting providers in 2025, where uptime and performance directly influence network reliability. When candidates internalize these foundational concepts, they develop the analytical perspective necessary to design resilient architectures capable of supporting enterprise workloads without compromising protection.
FortiOS Architecture And Administrative Control
FortiOS provides the operating framework powering FortiGate appliances, enabling administrators to manage interfaces, monitor resources, and enforce policy-based routing. Understanding both graphical and command-line interfaces improves operational flexibility and troubleshooting efficiency. Many professionals sharpen their technical literacy by following curated developer discussions highlighted in top Java blogs because exposure to engineering thought processes strengthens problem-solving abilities. Administrative competence ensures that security configurations remain aligned with organizational objectives while minimizing downtime during updates or maintenance cycles.
Security Fabric And Integrated Protection
Fortinet’s Security Fabric promotes an interconnected defense ecosystem where devices collaborate to share threat intelligence and automate responses. This architecture reduces the risk posed by fragmented security strategies and encourages proactive mitigation. Agile project leadership often supports these initiatives, reflecting structured workflows found within agile certification preparation that emphasize adaptability and continuous improvement. Administrators who understand integrated security models can deploy coordinated protections across endpoints, networks, and cloud services, creating a unified shield against sophisticated cyber threats.
Building Effective Firewall Policies
Firewall policies represent the operational heart of any FortiGate deployment because they dictate how traffic moves between network segments. Administrators must carefully define source and destination parameters, services, schedules, and inspection rules to ensure legitimate communication flows uninterrupted. Strategic planning techniques mirrored in project management certification paths help professionals structure policies logically, reducing configuration errors that might expose vulnerabilities. Thoughtfully arranged rule sets not only enhance security but also simplify long-term management as environments grow more complex.
Authentication Strategies And Access Control
User authentication adds a defensive layer by verifying identities before granting network privileges. Wireless infrastructure expertise complements this approach, particularly when reviewing enterprise connectivity principles covered within Ruckus certification tracks that highlight secure access design. FortiGate supports multiple authentication mechanisms, including directory services and multi-factor validation, allowing organizations to tailor security posture according to risk tolerance. Strong authentication frameworks prevent unauthorized entry while preserving seamless experiences for verified users.
Leveraging Automation And Cloud Integration
Automation continues to reshape cybersecurity operations by reducing manual workloads and accelerating response times. FortiGate administrators frequently integrate firewall management with cloud-based tools to streamline monitoring and orchestration. Customer relationship platforms discussed in Salesforce certification programs illustrate how automation enhances operational visibility across departments, reinforcing the value of interconnected systems. Candidates who understand automation principles gain a competitive advantage because they can deploy scalable defenses capable of adapting to fluctuating traffic demands.
Study Planning And Performance Techniques
Preparing effectively requires more than technical knowledge; it demands structured study habits and disciplined time management. Candidates benefit from adopting pacing techniques comparable to those of MCAT timing strategies, where endurance and concentration determine outcomes. Breaking study sessions into focused intervals improves retention while reducing cognitive fatigue. Regular self-assessment helps identify weak areas early, allowing candidates to refine preparation before exam day.
Virtualization And Secure Desktop Delivery
Modern enterprises frequently rely on virtual desktop environments to support distributed teams while maintaining centralized control. Understanding these infrastructures helps FortiGate administrators secure remote connections and enforce consistent policies regardless of user location. Architectural insights similar to those explored across Azure virtual desktop planning demonstrate how virtualization enhances flexibility without sacrificing governance. This knowledge prepares candidates to protect digital workspaces that extend beyond traditional office boundaries.
DevOps Awareness For Security Professionals
Security no longer operates separately from development workflows; instead, it integrates directly into continuous delivery pipelines. Administrators who understand DevOps culture can collaborate more effectively with engineering teams to embed protection earlier within deployment cycles. Foundational concepts highlighted across the DevOps fundamentals overview reinforce the importance of automation, monitoring, and iterative improvement. This cross-functional awareness enables FortiGate specialists to support innovation without introducing unnecessary risk.
Infrastructure Design Principles
Designing resilient infrastructure requires balancing scalability, redundancy, and cost efficiency while maintaining robust defenses. FortiGate deployments often form part of broader architectural strategies that prioritize high availability and intelligent traffic distribution. Professionals examining enterprise blueprints often reference frameworks explained in Azure infrastructure design to understand how layered systems support long-term growth. Candidates who appreciate these design philosophies can implement solutions that remain dependable even under heavy network loads.
Enterprise Analytics And Security Visibility
Data visibility plays a crucial role in identifying anomalies and preventing breaches. FortiGate logging capabilities enable administrators to analyze usage patterns, generate reports, and refine policy decisions based on measurable evidence. Analytical thinking parallels the methodologies of enterprise analytics architecture, where structured data evaluation drives informed strategy. By leveraging detailed insights, security teams can respond proactively rather than reacting after incidents occur.
Troubleshooting Methodologies That Work
Effective troubleshooting separates proficient administrators from average practitioners. Candidates must learn to interpret logs, isolate misconfigurations, and validate connectivity step by step until root causes emerge. Diagnostic discipline mirrors structured repair approaches associated with CompTIA troubleshooting skills that emphasize systematic evaluation rather than guesswork. Practicing these methods in lab environments builds confidence and prepares professionals to resolve disruptions quickly within production networks.
Performance Optimization Techniques
Security measures must operate efficiently to avoid slowing legitimate traffic. Performance optimization begins with evaluating inspection modes, balancing deep analysis with throughput requirements. Administrators should monitor resource utilization to ensure that firewall hardware supports current demand. Load distribution and intelligent routing further enhance responsiveness during peak activity. Regular performance assessments help teams anticipate capacity needs before congestion appears. By aligning protection with efficiency, organizations maintain a seamless user experience while preserving strong safeguards.
Security Awareness And Employee Engagement
Technology alone cannot guarantee protection; employees play a vital role in defending organizational assets. Security awareness programs educate staff about phishing risks, password hygiene, and safe browsing habits. Encouraging a culture of vigilance reduces the likelihood of accidental breaches. Clear reporting channels empower employees to share concerns promptly, allowing teams to investigate potential threats early. When awareness becomes part of everyday workflow, organizations benefit from a collective defense mindset that strengthens overall resilience.
Change Management In Security Environments
Change management ensures that updates occur without destabilizing infrastructure. Before implementing adjustments, administrators should evaluate potential impacts and schedule maintenance windows that minimize disruption. Transparent communication keeps stakeholders informed about upcoming modifications. Testing changes in controlled environments reduces the risk of unintended consequences. After deployment, reviewing outcomes confirms that objectives were achieved. A structured approach to change fosters trust across departments and supports consistent operational performance.
Strengthening Legacy Network Knowledge
Although cybersecurity evolves rapidly, legacy networking principles still influence many enterprise environments. Understanding earlier technologies helps administrators recognize compatibility challenges and migration requirements. Historical perspectives on classic networking certification remind candidates that modern innovations often build upon established protocols. This awareness encourages thoughtful upgrades that maintain service continuity while introducing stronger defenses.
Preparing For Long-Term Certification Growth
Achieving NSE4_FGT-7.2 often marks the beginning rather than the end of a professional development journey. Continuous learning ensures administrators remain capable of defending infrastructures against increasingly complex threats. Career progression benefits professionals who broaden foundational knowledge, similar to pathways network support certification, because diverse expertise enhances adaptability. By committing to ongoing education, candidates transform certification success into sustained professional relevance within the cybersecurity field.
Expanding Technical Depth For NSE4_FGT-7.2 Success
Advancing toward NSE4_FGT-7.2 mastery requires strengthening technical depth across hardware awareness, operating systems, and endpoint communication. Security administrators must recognize how devices interact at every layer of the network to prevent weak points from emerging unnoticed. Early computing principles continue shaping modern defense strategies, and many professionals revisit foundational concepts discussed within CompTIA hardware essentials to refine their understanding of device behavior. This clarity improves firewall configuration decisions and ensures that administrators can anticipate how infrastructure responds under varying workloads.
Operating System Awareness And Firewall Efficiency
Operating systems influence how traffic is generated, authenticated, and routed across enterprise networks. Administrators who understand system processes can create policies that complement rather than disrupt productivity. Diagnostic techniques explored across operating system support skills encourage structured thinking when evaluating compatibility concerns. By aligning firewall settings with endpoint behavior, professionals reduce latency while maintaining strong inspection standards, ultimately delivering a balanced user experience.
Endpoint Security And Network Entry Points
Endpoints often represent the first line of interaction between users and corporate infrastructure, making them attractive targets for attackers. Effective FortiGate deployments require awareness of how endpoint configurations affect authentication and session integrity. Knowledge-reinforced modern endpoint configuration highlights the importance of device readiness before granting network access. When administrators proactively address vulnerabilities at the endpoint level, they dramatically lower the probability of unauthorized intrusion.
Mobility, Connectivity, And Secure Access
Mobile devices and remote work have transformed connectivity expectations, requiring administrators to support seamless access without sacrificing control. Wireless protections and encrypted communication channels play critical roles in this balance. Lessons associated with secure mobility practices remind candidates that flexibility must coexist with vigilance. Implementing adaptive policies ensures that users remain productive regardless of location while the network continues enforcing strict verification standards.
Governance And Risk Management Principles
Governance frameworks guide organizations in establishing consistent rules for technology usage, data handling, and compliance adherence. FortiGate professionals benefit by aligning firewall strategies with broader governance models that define accountability across departments. Structured evaluation approaches emphasized in architecture governance certification illustrate how oversight strengthens operational transparency. When administrators integrate governance thinking into daily operations, they help organizations maintain trust and regulatory alignment.
Cloud Foundations And Security Responsibilities
Cloud adoption introduces shared responsibility models where providers manage infrastructure while customers secure configurations and access controls. FortiGate administrators frequently operate within hybrid ecosystems, making cloud literacy indispensable. Concepts presented across cloud technology associate emphasize scalability alongside disciplined configuration practices. Understanding these dynamics enables professionals to extend firewall protections beyond physical data centers into elastic environments without losing visibility.
Incident Response Planning
Preparedness determines how effectively an organization can contain cyber incidents. A structured incident response plan outlines roles, communication channels, and escalation paths before emergencies arise. FortiGate professionals should coordinate with leadership, legal teams, and IT departments to ensure that response efforts remain organized under pressure. Simulation exercises strengthen readiness by revealing procedural gaps that might otherwise go unnoticed. Rapid containment limits financial loss and reputational damage while supporting faster recovery. Ultimately, proactive planning transforms uncertainty into controlled action, empowering organizations to navigate disruptions with clarity.
Network Segmentation For Risk Reduction
Network segmentation divides infrastructure into smaller zones, preventing attackers from moving laterally if a breach occurs. Administrators can assign tailored policies to each segment, ensuring that sensitive assets receive stronger protection than general traffic areas. Segmentation also enhances performance by reducing unnecessary broadcast activity. Careful planning is essential so legitimate communication continues uninterrupted while restrictions remain effective. Over time, segmented environments prove easier to monitor because anomalies become more apparent within defined boundaries. This architectural approach supports both resilience and operational efficiency.
Backup Strategies And Recovery Assurance
Reliable backup strategies protect organizations against data loss caused by cyberattacks, hardware failure, or human error. Administrators should schedule automated backups and verify their integrity periodically to confirm successful restoration. Storing copies in separate locations adds an extra layer of protection against localized disruptions. Recovery planning should prioritize critical systems so essential services return online quickly. When backup procedures are integrated into daily operations, organizations minimize downtime and preserve business continuity even during unexpected events.
Advanced Security Analysis Techniques
Sophisticated threats demand analytical precision, encouraging administrators to evaluate patterns rather than isolated events. Behavioral monitoring, anomaly detection, and threat intelligence aggregation contribute to stronger defenses. Strategic approaches discussed advanced security analytics demonstrate how layered analysis improves incident response timelines. With refined analytical skills, FortiGate specialists can interpret signals quickly and implement countermeasures before disruptions escalate.
Strengthening Defense Against Distributed Attacks
Distributed denial-of-service attacks remain a persistent concern because they overwhelm infrastructure and degrade service availability. FortiGate solutions can integrate with upstream protections to absorb traffic surges and filter malicious packets. Defensive strategies AWS DDoS protection strategies reinforce the importance of multi-layered mitigation. Administrators who understand traffic shaping and rate limiting create resilient perimeters capable of maintaining uptime during hostile conditions.
Planning Secure Cloud Transitions
Organizations migrating enterprise workloads must evaluate compatibility, performance, and security simultaneously. Firewall administrators often participate in migration planning to ensure that segmentation policies remain intact after transition. Methodologies described within the SAP cloud migration strategy highlight the value of phased adoption supported by rigorous testing. Careful preparation prevents configuration gaps that could otherwise appear during large-scale moves.
Designing Private Network Environments
Virtual private clouds allow organizations to isolate workloads while preserving scalable connectivity. FortiGate devices frequently serve as gateways controlling traffic between private segments and public endpoints. Architectural clarity emerges when reviewing Amazon VPC fundamentals because segmentation remains central to effective defense. Administrators who design thoughtful address spaces and routing paths create environments where sensitive data remains shielded from unnecessary exposure.
Preparing For Technical Discussions And Evaluations
Security professionals often participate in technical interviews, audits, or architecture reviews where they must articulate decisions clearly. Confidence grows with exposure to scenario-based questioning similar to those AWS VPC interview questions. Practicing structured explanations ensures administrators can justify policy choices and demonstrate awareness of potential tradeoffs. This communication skill becomes particularly valuable when collaborating with executive stakeholders.
Building Scalable Network Blueprints
Scalability ensures that the infrastructure continues operating smoothly as user demand expands. Firewalls must accommodate growth without introducing bottlenecks or operational complexity. Design perspectives shared. AWS VPC overview guide emphasizes modular planning that supports incremental expansion. By applying these principles, FortiGate administrators can construct adaptable frameworks that evolve alongside organizational ambitions.
Database Security Awareness
Databases store mission-critical information, making their protection a top priority for security teams. Firewall segmentation, encryption enforcement, and access monitoring collectively safeguard these repositories. Professionals exploring cloud database engineering often learn how structured data environments demand meticulous permission models. Integrating database awareness into firewall policies prevents unauthorized queries while preserving legitimate analytics workflows.
Developer Collaboration And Secure Deployment
Security teams increasingly collaborate with developers to embed protection directly into application lifecycles. When administrators understand coding workflows, they can anticipate how applications communicate across ports and services. Insights discussed in cloud developer training illustrate the benefits of aligning infrastructure rules with application architecture. This partnership reduces friction during releases and ensures that security controls evolve alongside software innovation.
Automating Operations With DevOps Culture
Automation reduces repetitive tasks while enabling faster configuration updates across distributed systems. FortiGate administrators who embrace DevOps principles can implement policy adjustments with minimal disruption. Continuous improvement philosophies cloud DevOps engineering reinforce the importance of monitoring and iterative refinement. Automated workflows enhance consistency and free administrators to focus on strategic initiatives.
Network Engineering Expertise And Traffic Control
Traffic engineering requires both analytical foresight and technical precision. Administrators must evaluate bandwidth patterns, routing efficiency, and failover readiness to maintain stable connectivity. Professional development cloud network engineering demonstrates how structured design improves predictability. When FortiGate policies align with engineered pathways, organizations benefit from smoother performance and reduced downtime.
Establishing A Security-First Organizational Mindset
A security-first culture encourages every department to consider risk management as part of daily operations rather than a reactive obligation. Leadership support, employee awareness, and continuous evaluation collectively sustain this mindset. Best practices in cloud security engineering show how proactive planning strengthens enterprise resilience. Administrators who champion this philosophy help transform cybersecurity into a shared responsibility that supports long-term stability.
Advancing Toward Mastery In FortiGate Security
Reaching a high level of competence in FortiGate administration requires consistent refinement of analytical thinking and architectural awareness. Professionals preparing for NSE4_FGT-7.2 often expand their knowledge into data ecosystems because modern security decisions depend heavily on intelligent data interpretation. Exposure to structured pipelines highlighted within modern enterprise learning paths focused on professional data engineering strengthens the ability to interpret network telemetry and convert it into meaningful defensive actions. When administrators understand how data flows across platforms, they gain the foresight needed to anticipate risks before they evolve into operational threats.
Aligning Certification With Career Stability
Certifications frequently influence hiring decisions, yet long-term success depends on how effectively professionals apply their knowledge within dynamic environments. Security administrators benefit from evaluating expectations realistically, particularly when considering perspectives outlined in PMP employment outcomes that clarify how credentials support opportunity rather than guarantee it. The NSE4_FGT-7.2 credential works best when paired with practical experience, communication skills, and adaptability. Employers seek individuals capable of protecting infrastructure while contributing to organizational strategy, making continuous development essential.
Selecting Complementary Professional Pathways
Building a well-rounded career often involves combining security expertise with project leadership abilities. Professionals who evaluate options presented in detailed industry decision-making guides about project certification comparison can better determine which frameworks align with their ambitions. FortiGate specialists frequently lead deployment initiatives, coordinate upgrades, and collaborate across departments, all of which benefit from structured management methodologies. Integrating leadership knowledge ensures that technical improvements translate into measurable organizational value.
Measuring Outcomes With Clear Success Indicators
Security projects demand clarity regarding expected outcomes so teams can evaluate effectiveness objectively. Administrators responsible for firewall rollouts must distinguish between baseline acceptance and broader performance achievements, a concept clearly explained in comprehensive professional evaluation standards covering acceptance versus success criteria. Establishing measurable benchmarks helps organizations validate that controls operate as intended while supporting operational continuity. This disciplined approach prevents ambiguity and reinforces accountability across implementation stages.
Exploring Broader Certification Ecosystems
Professional growth often accelerates when individuals understand how various credentials complement one another. Security practitioners reviewing options highlighted in PMI certification pathways frequently discover opportunities to expand leadership capabilities alongside technical expertise. A diversified certification strategy enhances credibility and demonstrates commitment to lifelong learning. For FortiGate administrators, this combination strengthens both strategic influence and operational authority.
Continuous Monitoring And Threat Visibility
Continuous monitoring enables organizations to detect suspicious behavior before it escalates into serious incidents. FortiGate administrators should establish real-time alerting systems that track unusual traffic patterns, unauthorized login attempts, and configuration changes. Visibility improves when logs are centralized and reviewed regularly, allowing teams to identify trends rather than isolated anomalies. Effective monitoring also supports faster incident response because administrators already possess contextual awareness. By maintaining persistent observation across network layers, security teams strengthen their defensive posture and reduce operational uncertainty while ensuring that protective controls remain aligned with evolving threat landscapes.
Configuration Management Best Practices
Configuration management plays a crucial role in maintaining stable and secure firewall operations. Administrators should document every policy adjustment, firmware update, and architectural modification to prevent confusion during audits or troubleshooting sessions. Standardized templates help ensure consistency across deployments, particularly in multi-site environments. Periodic reviews confirm that outdated rules no longer expose vulnerabilities. Strong configuration discipline also simplifies recovery after unexpected disruptions because teams can quickly restore verified settings. When organizations treat configuration as a strategic process rather than a routine task, they cultivate reliability and long-term operational confidence.
Strategic Thinking For Complex Evaluations
High-stakes exams reward candidates who approach challenges with structured reasoning rather than impulsive decision-making. Analytical preparation methods outlined in advanced logical reasoning frameworks designed for exam readiness, like LSAT strategic preparation, highlight the value of logical sequencing and careful interpretation of scenarios. Applying similar discipline when studying firewall behaviors allows candidates to recognize subtle distinctions between configuration choices. Over time, this method builds confidence that extends beyond testing environments into real-world troubleshooting.
Virtual Application Delivery And Secure Access
Enterprises increasingly depend on virtual application delivery platforms to support distributed teams while maintaining centralized governance. Security administrators who explore concepts presented in modern enterprise virtualization training pathways covering Citrix virtualization associate gain insight into how traffic flows between users and hosted applications. Integrating FortiGate controls within these ecosystems ensures encrypted communication and consistent authentication policies. Understanding virtual delivery models also prepares professionals to manage bandwidth intelligently as user demand fluctuates.
Managing Advanced Virtualization Environments
As organizations expand virtualization initiatives, administrators must maintain visibility across layered infrastructures. Skills reinforced across Citrix advanced administration emphasize the importance of monitoring session behavior and enforcing segmentation. FortiGate appliances complement these environments by filtering traffic and identifying anomalies before they escalate. Professionals who master both virtualization and firewall governance create ecosystems where performance and protection coexist harmoniously.
Supporting Collaborative Digital Workspaces
Modern workplaces rely on collaboration platforms that enable teams to operate seamlessly regardless of location. Knowledge connected to Citrix workspace management illustrates how centralized environments simplify administration while supporting productivity. Embedding firewall inspection within these platforms protects shared data without interrupting communication. Security professionals who understand collaboration technologies can craft policies that preserve efficiency while maintaining strict oversight.
Engineering Reliable Application Performance
Application performance directly affects user satisfaction and operational continuity, making proactive monitoring essential. Techniques associated with Citrix performance engineering highlight the value of capacity planning and predictive analysis. FortiGate administrators contribute by optimizing inspection paths and minimizing latency wherever possible. This balanced approach ensures that protective measures remain effective without creating unnecessary delays for legitimate traffic.
Secure Remote Connectivity At Scale
Remote connectivity has become a defining characteristic of contemporary enterprise architecture. Administrators examining frameworks related to advanced enterprise network protection strategies centered on Citrix secure connectivity learn how encrypted tunnels and identity validation protect distributed users. FortiGate VPN capabilities align naturally with these principles, offering scalable access without compromising oversight. As remote participation continues expanding, expertise in secure connectivity positions professionals as essential contributors to organizational resilience.
Ethical Awareness In Security Practice
Technical ability must always align with ethical responsibility because administrators often manage sensitive data and critical infrastructure. Professional standards outlined in globally recognized cybersecurity responsibility training aligned closely with ethical hacking foundations remind practitioners that integrity underpins trust. Applying ethical judgment when configuring monitoring tools or analyzing traffic ensures respect for privacy while safeguarding assets. Organizations increasingly prioritize professionals who demonstrate both competence and principled decision-making.
Governance, Compliance, And Policy Alignment
Regulatory expectations continue evolving, requiring organizations to demonstrate consistent adherence to defined policies. Security leaders who review frameworks supported by enterprise regulatory strategy models associated directly with governance risk compliance understand how structured oversight reduces exposure to legal and operational consequences. FortiGate deployments should align with documented controls so audits proceed smoothly. Establishing repeatable processes strengthens transparency and reassures stakeholders that defenses remain dependable.
Data Platforms And Defensive Intelligence
Data platforms generate insights capable of transforming reactive security postures into predictive strategies. Administrators exploring distributed processing ideas highlighted in large-scale analytics infrastructure training aligned strongly with Cloudera data administration, often recognizing how analytics reveal subtle anomalies across vast traffic volumes. Integrating these insights with firewall alerts allows teams to respond more quickly to irregular behavior. Over time, intelligence-driven defense becomes a cornerstone of mature cybersecurity programs.
Harnessing Data Science For Threat Detection
Data science techniques enhance pattern recognition, enabling administrators to detect deviations that might otherwise remain hidden. Concepts presented in modern predictive analytics education, designed specifically around data science foundations, demonstrate how statistical modeling supports proactive defense strategies. When FortiGate telemetry feeds analytical engines, organizations gain a clearer understanding of behavioral trends. This synergy between analytics and security equips teams to anticipate threats rather than merely reacting after damage occurs.
Hardware Literacy And Network Reliability
Even within cloud-forward environments, hardware awareness remains vital because physical components still influence throughput and redundancy. Reviewing principles explained in core computing infrastructure knowledge areas, strongly emphasizing CompTIA hardware fundamentals, reinforces the relationship between device capability and firewall efficiency. Administrators who appreciate hardware limitations can design architectures that avoid bottlenecks while supporting inspection demands. Reliable infrastructure ultimately forms the backbone of effective cybersecurity.
Sustaining Long-Term Professional Growth
True expertise emerges from continuous refinement rather than isolated achievements. FortiGate professionals who commit to ongoing education, interdisciplinary awareness, and adaptive thinking remain prepared for future technological shifts. By blending leadership insight, analytical capability, and technical mastery, administrators transform certification knowledge into strategic influence. The NSE4_FGT-7.2 journey, therefore, represents more than exam preparation; it marks the beginning of a career defined by resilience, curiosity, and a dedication to safeguarding the digital world.
Conclusion
Preparing for the NSE4_FGT-7.2 certification represents far more than the pursuit of a professional credential; it marks a commitment to mastering the principles that sustain modern cybersecurity infrastructures. Throughout this guide, the emphasis has remained on building a balanced combination of technical expertise, analytical awareness, and strategic thinking. FortiGate administrators operate at the center of organizational defense, where every configuration decision influences both protection and performance. Achieving proficiency, therefore, requires continuous learning, disciplined preparation, and the ability to interpret complex network behaviors with confidence.
A strong foundation in networking concepts establishes the groundwork for advanced firewall management. Understanding how data moves across environments allows professionals to implement policies that protect assets without disrupting essential operations. As infrastructures expand across hybrid and cloud ecosystems, administrators must remain adaptable, ensuring that security controls evolve alongside technological innovation. This adaptability becomes a defining characteristic of successful professionals, enabling them to anticipate challenges rather than reacting after vulnerabilities appear.
Equally important is the development of structured problem-solving abilities. Security environments rarely present predictable scenarios, and administrators are frequently called upon to troubleshoot under pressure. Methodical evaluation, supported by clear documentation and thoughtful configuration practices, helps transform uncertainty into manageable processes. When professionals approach challenges with logic and patience, they reduce downtime and reinforce organizational stability.
The modern cybersecurity landscape also demands collaboration. Firewall specialists do not operate in isolation; they coordinate with developers, infrastructure engineers, compliance teams, and executive leadership. Effective communication ensures that security initiatives align with broader business objectives while maintaining transparency across departments. Professionals who cultivate interpersonal skills alongside technical knowledge often emerge as trusted advisors capable of guiding long-term strategy.
Ethical responsibility further strengthens the role of a security professional. Access to sensitive systems requires integrity, discretion, and respect for privacy. Organizations depend on administrators who recognize the weight of this responsibility and act with accountability in every decision. Upholding ethical standards not only protects data but also fosters trust among stakeholders, customers, and partners.
Another recurring theme in the certification journey is the importance of measurable outcomes. Security strategies must demonstrate effectiveness through clear benchmarks and continuous evaluation. Whether optimizing performance, refining segmentation, or enhancing monitoring practices, administrators should rely on evidence-based improvements rather than assumptions. This results-oriented mindset supports sustainable growth and ensures that defenses remain aligned with evolving risks.
Long-term success also depends on embracing a culture of continuous improvement. Cyber threats shift rapidly, driven by technological advancement and increasingly sophisticated adversaries. Professionals who remain curious and proactive position themselves ahead of these changes. Ongoing education, experimentation, and engagement with emerging ideas help transform foundational knowledge into enduring expertise.
Leadership potential naturally grows from this dedication to development. As administrators gain experience, they often influence organizational direction by recommending architectural enhancements and guiding risk management initiatives. The ability to connect technical insights with strategic priorities elevates their impact, allowing them to contribute meaningfully to resilience and innovation.
Ultimately, the NSE4_FGT-7.2 path symbolizes a broader professional evolution. It encourages individuals to think critically, act responsibly, and pursue excellence in every aspect of security practice. By combining technical mastery with adaptability, collaboration, and ethical awareness, professionals prepare themselves not only to succeed in certification but also to safeguard the digital environments that power modern enterprises. The journey does not end with passing an exam; instead, it opens the door to a career defined by vigilance, growth, and the ongoing pursuit of cybersecurity excellence.
Choose ExamLabs to get the latest & updated Fortinet NSE4_FGT-7.2 practice test questions, exam dumps with verified answers to pass your certification exam. Try our reliable NSE4_FGT-7.2 exam dumps, practice test questions and answers for your next certification exam. Premium Exam Files, Question and Answers for Fortinet NSE4_FGT-7.2 are actually exam dumps which help you pass quickly.
How to Open VCE Files
Please keep in mind before downloading file you need to install Avanset Exam Simulator Software to open VCE files. Click here to download software.
Related Exams
- NSE4_FGT_AD-7.6 - Fortinet NSE 4 - FortiOS 7.6 Administrator
- FCSS_EFW_AD-7.6 - NSE 7 - Enterprise Firewall 7.6 Administrator
- FCP_FGT_AD-7.6 - FCP - FortiGate 7.6 Administrator
- FCP_FMG_AD-7.6 - Fortinet NSE 5 - FortiManager 7.6 Administrator
- FCSS_NST_SE-7.6 - Fortinet NSE 6 - Network Security 7.6 Support Engineer
- FCSS_LED_AR-7.6 - Fortinet NSE 6 - LAN Edge 7.6 Architect
- FCP_FAZ_AN-7.6 - Fortinet NSE 5 - FortiAnalyzer 7.6 Analyst
- NSE5_SSE_AD-7.6 - Fortinet NSE 5 - FortiSASE and SD-WAN 7.6 Core Administrator
- FCP_FCT_AD-7.4 - Fortinet NSE 6 - FortiClient EMS 7.4 Administrator
- FCP_FWF_AD-7.4 - FCP - Secure Wireless LAN 7.4 Administrator
- NSE5_FSW_AD-7.6 - Fortinet NSE 5 - FortiSwitch 7.6 Administrator
- FCP_FSM_AN-7.2 - FCP - FortiSIEM 7.2 Analyst
- FCSS_SASE_AD-25 - FCSS - FortiSASE 25 Administrator
- FCP_FWB_AD-7.4 - FCP - FortiWeb 7.4 Administrator
- NSE7_SSE_AD-25 - Fortinet NSE 7 - FortiSASE 25 Enterprise Administrator
- NSE7_SOC_AR-7.6 - Fortinet NSE 7 - Security Operations 7.6 Architect
- NSE5_FNC_AD-7.6 - Fortinet NSE 5 - FortiNAC-F 7.6 Administrator
- NSE6_SDW_AD-7.6 - Fortinet NSE 6 - SD-WAN 7.6 Enterprise Administrator
- FCP_FML_AD-7.4 - FCP - FortiMail 7.4 Administrator
- NSE4_FGT-7.0 - Fortinet NSE 4 - FortiOS 7.0
- FCSS_CDS_AR-7.6 - FCSS - Public Cloud Security 7.6 Architect
- FCSS_EFW_AD-7.4 - FCSS - Enterprise Firewall 7.4 Administrator
- FCSS_SDW_AR-7.6 - FCSS - SD-WAN 7.6 Architect
- NSE6_FSR-7.3 - Fortinet NSE 6 - FortiSOAR 7.3 Administrator
- FCP_FGT_AD-7.4 - FCP - FortiGate 7.4 Administrator
- NSE7_OTS-7.2 - Fortinet NSE 7 - OT Security 7.2
- NSE6_FSW-7.2 - Fortinet NSE 6 - FortiSwitch 7.2
- FCSS_NST_SE-7.4 - FCSS - Network Security 7.4 Support Engineer
- NSE4_FGT-6.4 - Fortinet NSE 4 - FortiOS 6.4
- NSE6_FWF-6.4 - Fortinet NSE 6 - Secure Wireless LAN 6.4
- NSE6_OTS_AR-7.6 - Fortinet NSE 6 - OT Security 7.6 Architect
- NSE6_EDR_AD-7.0 - Fortinet NSE 6 - FortiEDR 7.0 Administrator
- FCP_FAZ_AN-7.4 - FCP - FortiAnalyzer 7.4 Analyst
- NSE5_FMG-7.2 - Fortinet NSE 5 - FortiManager 7.2
- FCSS_SDW_AR-7.4 - FCSS - SD-WAN 7.4 Architect
- FCP_FCT_AD-7.2 - FCP - Forti Client EMS 7.2 Administrator
- FCP_FAZ_AD-7.4 - FCP - FortiAnalyzer 7.4 Administrator
Enter Your Email Address to Proceed
Please fill out your email address below in order to purchase Certification/Exam.
Provide Your Email Address To Download VCE File
Please fill out your email address below in order to Download VCE files or view Training Courses.
-
Trusted By 1.2M IT Certification
Candidates Every Month
-
VCE Files Simulate Real exam
environment
-
Instant download After
Registration